Ever since reading Cory Doctorow’s “Makers“, I was excited about the idea of being able to tag my belongings with small electronic devices that would flash and beep to enable me to locate them.
There were some devices already available, like the Loc8tor range of products. However, battery life was poor (2-5 months typical), feature set was limited, and they were still quite large.
So when I saw the StickNFind project on IndieGoGo (a crowd funding site, similar to KickStarter), I was really excited. Ultra-small (probably the size of some arbitrary US denominated coin I am wholly unfamiliar with), long battery life (1 year typical), 100 ft range, and uses an iPhone or Android phone to locate them. Perfect! I signed up for 4 of them.
They turned up yesterday, and it appears I am one of the first people to get hold of them. Unfortunately, it appears that not all is well in StickNFind land.
They came well packaged in a cardboard box, with the four tags stuck onto a piece of cardboard. The instructions noted that I may need to “tap it 4 times with your finger or with a pen” to wake it up. I tried gently tapping the first one I peeled off, and nothing happened. Then I tried harder. Still nothing. I checked for one of those small plastic tabs that you need to pull out to activate a battery. Nothing.

An open and closed StickNFind
I peeled a second one off. This one responded after a few taps with a flash and a beep. So did the third, and fourth. Looks like the first one is dead.
I then downloaded the app onto my iPhone 5. This is the latest v1.1 app.
The three tags paired fairly quickly with my phone with the default text tags of “sNf – 0”, “sNf – 1”, “sNf – 3”. They kind of showed up on the radar view, but the range was showing big numbers in the range of 100 (feet? inches? cm? m? the axis is not labelled).
When they are showing on the radar screen, you can make them beep, flash or do both. For some reason, only tag 0 and 1 would do this. 3 was showing on the screen, and the beep/flash buttons were present, but it wouldn’t respond.
I found out the app makes you accept the EULA each time you start it, and crashes very frequently.
I then tried the “Find It” feature. I turned this on for tag 0. It immediately said that the tag had been found. I turned it on for tag 1. The tag beeped and flashed a few times, and told me it had been found. Operation seemed intermittent with all three tags.
Back to the radar, and I found that the three tags, despite being adjacent to each other, were showing at ranges varying from a couple of units to a hundred or more. They kept on moving around, despite the tags and phone being stationary.

Not working so well – none show up despite being next to the phone
I opened the fourth tag and reseated the battery. This time it showed up on the iPhone, but as a “StickNFind – 0” – why is this name different to the others?

Why is the name different for one tag?
All the while, on the radar page, the tags were dancing back and forth like a loon on speed. I couldn’t see how the leash functionality (where you are warned that the tag has moved away from you) would work.
I looked at the temperature screen. One was showing 11degC, another 22degC. It does say you may need to wait. So I waited until morning.
Next morning, tag “sNf – 3” had completely stopped responding. The others were intermittent – I couldn’t seem to wake them. The temperatures were still wildly different, despite being in a centrally heated space next to each other.
I thought I would test the range. Even across our small open downstairs space, they would all drop out now and then. I went upstairs and none of them would work, and it is only a wooden floor.
I attached one tag to my keys. I took them to work and back again, and found that it didn’t work for most of the day. It briefly worked in my office, but the range was less than 30ft.
Once home, I found that I couldn’t get any of the tags working at all. One of them beeped and flashed a significant time after it was asked to. I reseated several of the batteries and checked they were dead, but still no luck.
I thought maybe my phone was at fault (although it works with other Bluetooth devices), so I tried my “new iPad”. I managed to pair it with one of the tags, but could get the tag to do nothing useful.
I checked the batteries using a multimeter, and all are showing 3V as expected.

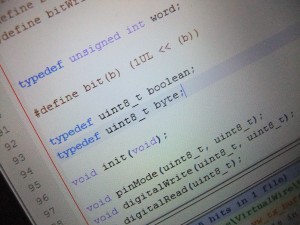
Detail of inside the tag
So – my first impressions:
- Tags don’t seem to work most of the time
- Range isn’t reliable
- Leash functionality is unusable as a result
- Temperature readings are way off and vary from device to device
- App crashes frequently and has many quirks
Really not good. I approached @StickNFind on twitter and found they suggested I call them in the US. I requested email, as a call would cost me a fair amount. No response. Website just has a contact form, no email address.
Since then, a few others have posted comments on IndieGoGo suggesting similar problems:
My stickers are going haywire, they all interfere with each other and 2.4ghz sources in the house (wifi, other Bluetooth devices). Basically if I pair my iPhone 5 to a sticker in my wallet and set the leash to “out of range”, it will beep constantly as I walk past RF noise sources. 2 stickers push the range of both back dozens of feet and they take turn being connected. Useless.
Sad to say these are not very good :( really want them to be but they just don't work very well, for example they keep loosing pairing so when you try to find item, even if on my lap, it can't find it. The app doesn't work well and is quite confusing for example what is zooming and why does it show direction if its only distance? Every time you open it you have to agree to the terms. I appreciate its an early product but I think should have kept it for a bit longer to make it fully work prior to release. Like I said I love the concept just wish it worked!
just received my two stickers and they both will not activate upon multiple tries at tapping. Needs to be replaced
So far, I am really not impressed. Unfortunately, I also backed the BluTracker project by the same guys. I don’t know if this is a problem with my specific devices, or the product as a whole. I hope they respond.
Note – please don’t bitch about crowd funding being a risk etc. They have delivered a product that doesn’t seem to work and it is being sold to people not on IndieGoGo now.