Again, browsing telnet, I see the word “ANPR” – Automatic Number Plate Recognition.
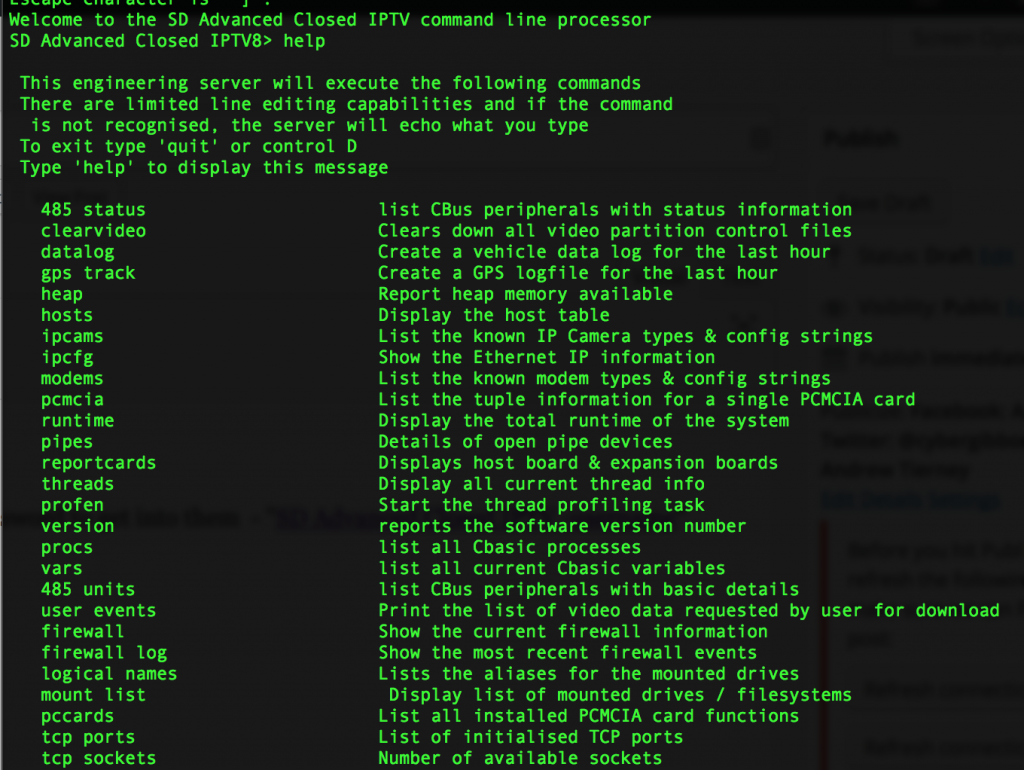
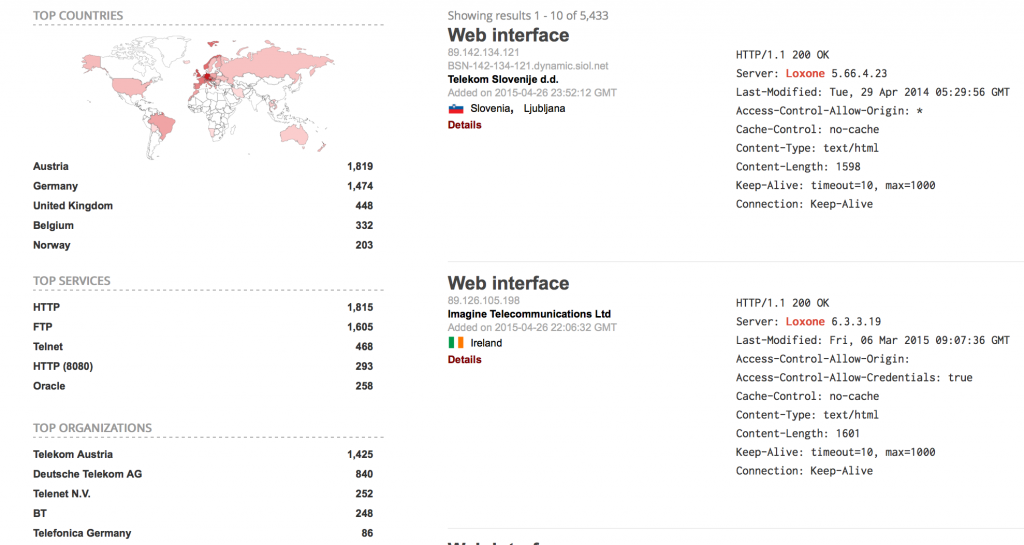
Most of these say “P372” and a Shodan search for that delivers the goods. The telnet prompt shows us P372, but nearly all of these also have HTTP open as well.
It’s safe to say a lot of these don’t have any authentication on telnet or HTTP.
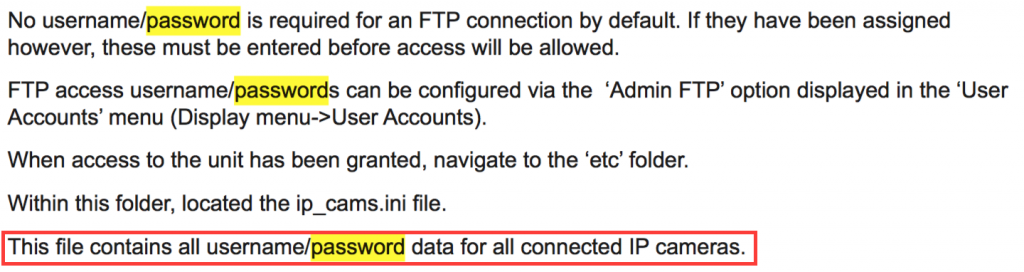
Their default mechanism to report plates is by FTPing the data to a central server. The FTP server IP and credentials can be viewed through the configuration interface. The manual recommends that this FTP acount has read and write permissions using MS FTP, so once you have these credentials, it is likely you can tamper or upload fake records – and not just for this single camera, but likely any in the network. The manual also uses the example “ftp_boot” for both user and pass, and it seems a lot of people have taken this literally.
These ANPR cameras are used by local authorities and governments.
Pff.
Who is to blame here?
I think the mnaufacturer should make the system impossible to configure this badly, and provide a default configuration and documentation that prevents this kind of stuff.
But whoever installed these also needs to bear some responsibility. If I get a boiler fitted, I expect the installer to know what each pipe and wire does, and not just hide the ones he doesn’t understand…
It looks like Darius Freamon has already found this.