I’m going to start a new series of posts, highlighting interesting Shodan searches I have seen in the last few weeks. Then maybe myself, or someone else, can take a better look at the devices and see if they can spot any problems.
Note that some of the search queries may require you to have an account on Shodan.
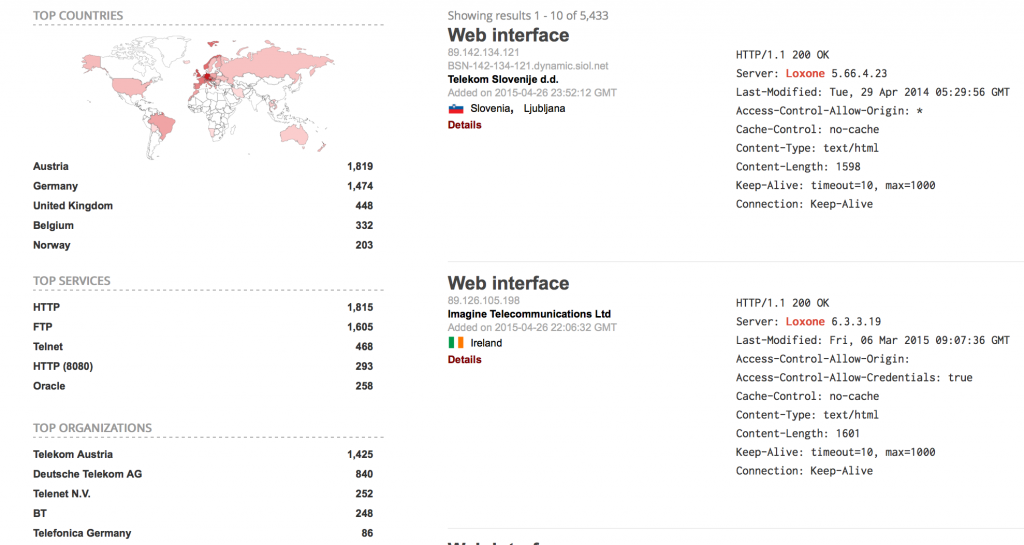
Loxone Miniserver
The simple search term for Loxone brings back a lot of results:
What can we see?
- These are all HTTP, FTP, telnet. Not HTTPS, SFTP/FTPS, or SSH. There is no excuse for running the non-secure versions of these protocols today.
- There is a lot of port-forwarding here, opening up access to these boxes.
- The spread of version numbers is wide, from 5.49.3.4 to 6.3.3.19 – likely that there is no automatic firmware update mechanism.
- The “Server” header of “Loxone” is not one of the commonly available HTTP daemons. Rolling your own HTTP server generally means bugs galore.
You can download their software “Loxone Config” from their site. A very cursory glance over it shows the following:
- No use of HTTPS anywhere.
- There is a config facility which sends to broadcast on the local network – port 7070 – which isn’t authenticated or filtered in anyway.
- They run a “cloud” service, part of which maps the MAC address of the device to an IP address, allowing enumeration of valid MACs (dns.loxonecloud.com/504F94000000 for example).
- The firmware is distributed with the software, including what looks like the web pages for the interface.
- The software opens up a number of ports in the 7xxx range on the local machine
It’s worth having a dig around anyway.
Security issues reported by Symantec.
April 29, 2015 at 11:12am[…] the findings in this report: » Interesting Shodan searches: Loxone Miniserver also taken into […]