Last time we powered up a board to see what it did just by observing the normal IO with our eyes.
This time we are going to look at what happens in more detail with this particular board using a logic analyser.
First things first, we’ll take the EEPROM out, pop it into our Bus Pirate EEPROM reader, pass the data through our converter, and then open the resulting .prm file in the CS2364 Windows utility.
This indicates that this board only has GPRS and PSTN paths enabled – no LAN.
There isn’t much else of note.
Running the .prm file through the strings utility we wrote provides very similar output to before – the same IP addresses and possibly the same password.
We now need to work out exactly what we want to connect to the logic analyser. The Dualcom has convenient test points grouped in threes and labelled GSM, PSTN, LAN and 485. It’s highly likely that these are serial connections – GND, TX, RX. A quick check of data sheets and use of the continuity tester confirms this.
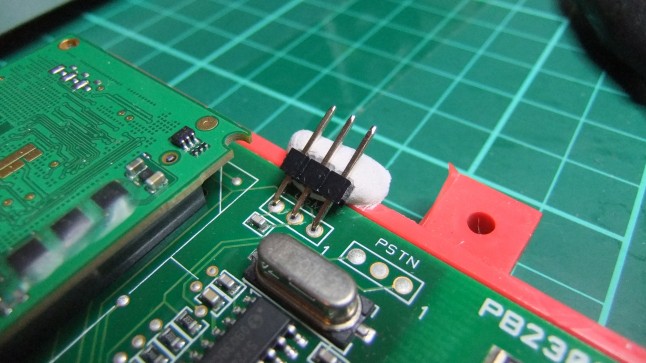
Let’s solder some pin headers onto GSM serial, PSTN serial and also the socketed EEPROM. Pin headers make connecting and reconnecting the logic analyser very quick and easy compared to using test hooks.
We already know what is on the EEPROM, but we don’t know when and how the data is accessed – using a logic analyser will allow us to see this. This could be compared to static analysis (reading out the EEPROM entirely) and dynamic analysis (seeing how the EEPROM is accessed).
Often test points on hardware end up full of solder due to the manufacturing process. It’s awkward to remove this solder, so I just tend to tack pin headers on at a slight angle. To hold these, I use White Tack – a bit like Blu-Tak but holds out at soldering temperatures. Much easier than using helping hands or pliers.
Yep – the joints look dry. Lead-free solder + leaded solder seems to result in joints looking like this.
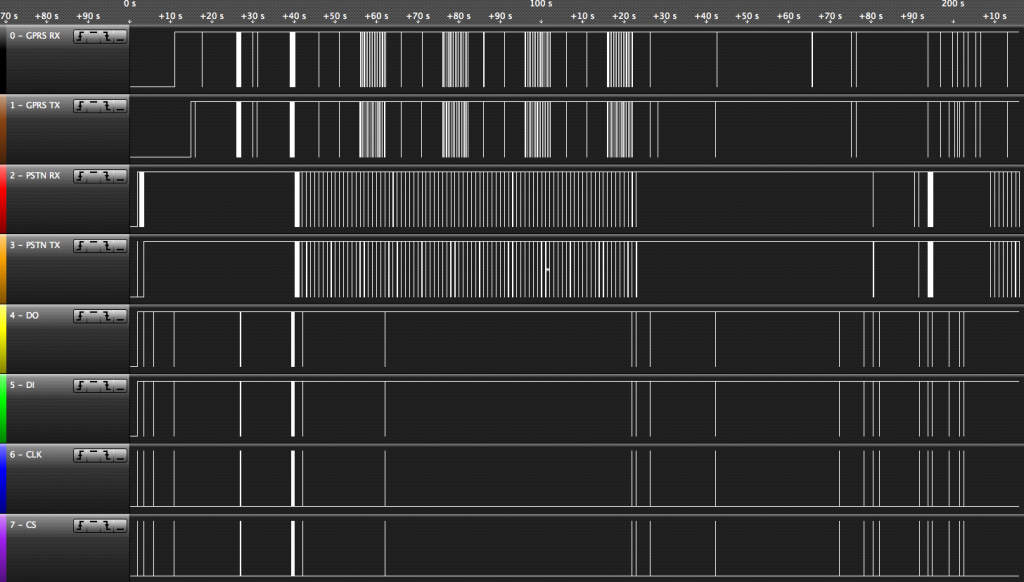
Once this is done, we connect up the logic analyser – the Saleae Logic. This is a USB logic analyser, and probably my most used reverse engineering tool. It is only 8-channel, but this is frequently more than adequate.
The connections end up as follows:
- 1 (Black) GPRS RX
- 2 (Brown) GPRS TX
- 3 (Red) PSTN RX
- 4 (Orange) PSTN TX
- 5 (Yellow) DO EEPROM
- 6 (Green) DI EEPROM
- 7 (Blue) CLK EEPROM
- 8 (Purple) CS EEPROM
- GND (Grey) GND
I don’t have enough channels to monitor CS for the soldered on EEPROM. We’ll have to look at that another day.
Yes – GND is grey and channel 1 is black on the Saleae Logic. This has caught more than a few people out!
After a few trial runs, I find out that I can use the following settings for analysing the data:
- GPRS RX/TX – 9600baud serial
- PSTN RX/TX – 2400baud serial
- EEPROM – SPI, CS active high, 30bits transferred
So now we have a good logic trace. At an overview level, you can see that everything is accessed at one point or another.
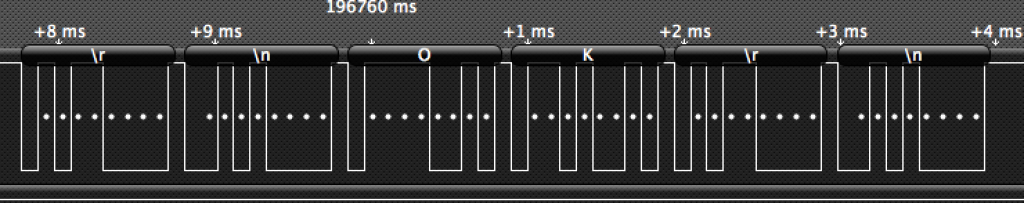
If we zoom in we can see EEPROM data transfers (this is a read – 0b110 is the command):
And a GPRS modem response:
And the modem as well:
You can download the settings/data for this trace here. This can be opened in the freely downloadable Saleae Logic program.
The next step is to decode some of this data further and see what is going on.