Update
The director of IT from Securtek got in touch via the contact form. They are working to fix these issues, and his response was measured and reasonable, especially in light of my rather inflammatory blog post.
Introduction
Another security industry website, another slew of basic mistakes.
SecurTek are a Canadian company who offer alarm monitoring. Even just a cursory glance at their system shows that they are ignoring basic security principles.
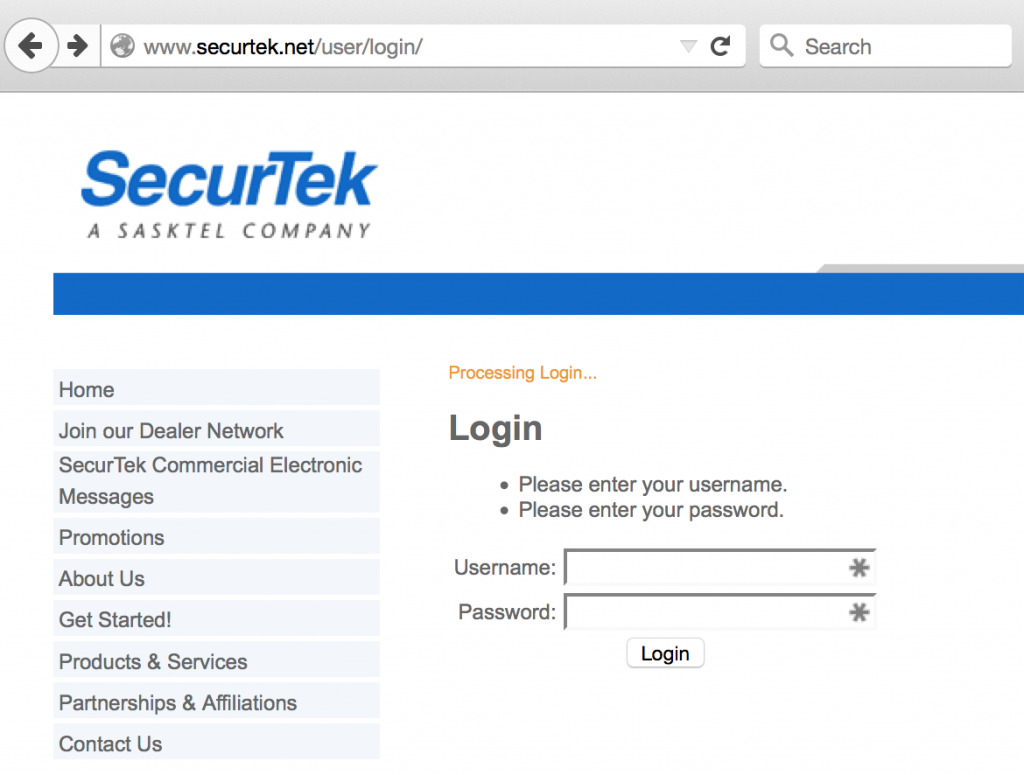
No HTTPS
The login page is lacking HTTPS. There is no excuse for this in 2015 for a commercial web service of any form.
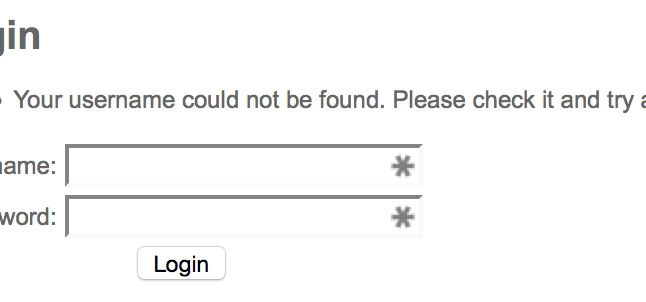
Username enumeration
The login form responds different depending on if the user exists or not.
This might seem minor, but it massively facilitates brute-forcing usernames and passwords by removing one of the unknowns. Best practice is to indicate that you have entered an incorrect username or password.
Passwords are stored in the plain
The forgotten password functionality simply emails you the password you have already set.
This has several implications.
It means that your password is stored in a way in which it can be retreived. Whilst it may be encrypted, this encryption can be reversed, yielding a password. This is not good and nowhere near best practice. Passwords should be hashed at the bare minimum, which prevents them being recovered in this way.
Email is not a secure way of delivering a password. There is the potential for many people to see this password. With password re-use being common, obtaining the password for SecurTek could yield access to many other systems. A password reset mechanism should use a random token and be time-limited.
Conclusion
This is a 2-minute glance at security, and it’s shown two very serious issues and one reasonably serious. They aren’t subtle issues.
Would you trust a company with your alarm monitoring if they can’t do these things right?