DVRs (Digital Video Recorders) are interesting targets for hardware hacking. They are generally powerful Linux machines with multiple network interfaces and have historically been full of vulnerabilities.
Identifying the security-relevant components on a DVR board make it far easier to quickly attack and gain access to the various interfaces: serial ports and SPI flash memory being the most important. We can also quickly isolate areas of the board that are not of interest; power supply, RAM, video ADCs, HDMI etc.
Disassembly and Powering
I would recommend removing the main PCB from the case to make access and inspection easier. Nearly all DVRs run on 12V, with a few running on 48V. Less than 120VDC and 50VAC is classified as SELV (Separated Extra Low Voltage) in the UK and is safe to work on in electrical shock terms. These low-voltages are still capable of causing heat, smoke and fire if shorted.
You do not need to have the hard drives connected when working on the DVRs. For 99% of DVRs, the drives only store footage, no operating system or configuration. Disconnect them, especially if you want to recover footage from them.
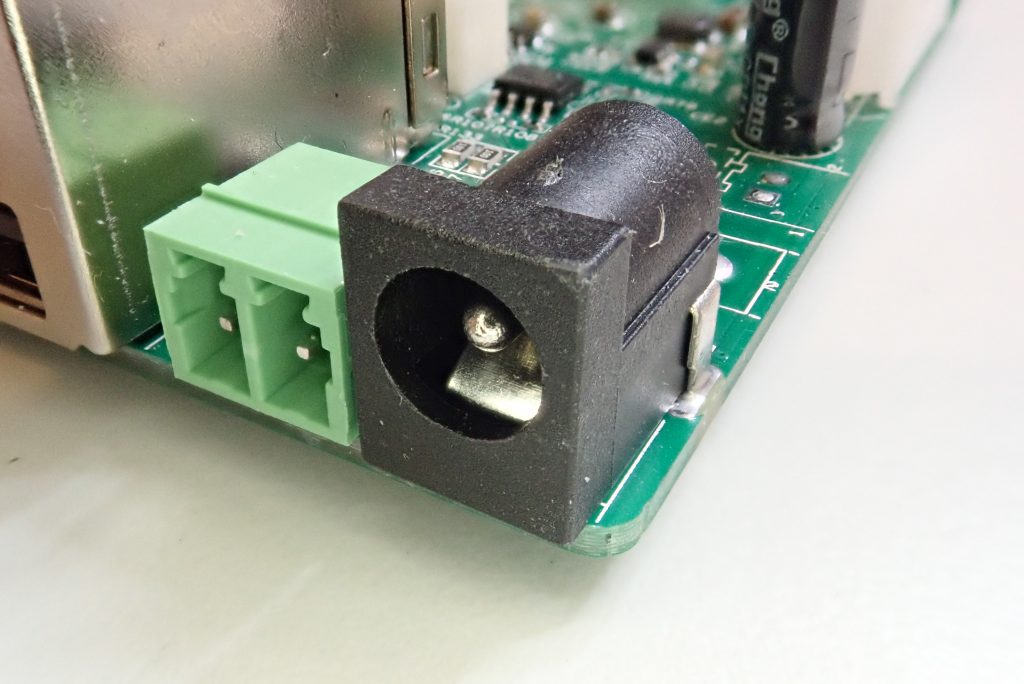
For nearly all 12V DVRs, a barrel jack power connector is used.
You can use the provided wall-wart style power supply but be warned that the quality and safety of many is in question. You can use a better quality power supply, but check that:
- The voltage matches. This should be a direct match – a 12V power supply for a 12V device.
- It can supply enough current. The replacement should be able to supply more current e.g. a 2A supply is suitable to replace a 1A supply. A DVR without drives will generally only consume a fraction of the power needed during normal operation.
- The polarity matches. Nearly all DVRs are centre positive. You can check this by looking for the pictogram on the original power supply.
The power supply below is 12V, maximum 2000mA (2A), DC (the straight line above dots) and centre positive.
Personally, I use a bench power supply when working on them, as this allows me to limit the amount of current provided. Simply chop the barrel jack off the end of an existing power supply and use this.
Many DVRs will have a heatsink on the main chip. This can make finding out the part number difficult, or finding out where pins go to. You can often remove it with careful levering. Generally, because we will be running the DVR without video feeds, the chip will not get hot enough to need a heatsink. As a rule of thumb, if you can’t touch the chip for more than a few seconds, it is too hot.
High-level Overview
Many of the low-cost DVRs are based around a Hisilicon chipset. These are large, powerful ARM SoCs (System-on-Chips) containing a wide array of peripherals.
SPI Flash
They tend to use SPI (Serial Peripheral Interface) NOR flash memory for storing the firmware and configuration. These range from 8Mbytes to 64Mbytes in size. This is a particularly convenient flash memory format for the reverse engineer.
Firstly, most of them are packaged in 8-pin SOIC (Small Outline Integrated Circuit). This is a comparatively large package, with the pins being accessible and 1.27mm apart. This makes physical access to the signals easy.
Secondly, the SPI interface is very simple. There are only 4 signal wires:
- DI (Data In) or MOSI (Master Out, Slave In)
- DO (Data Out) or MISO (Master In, Slave Out)
- CS (Chip Select)
- CLK (Clock)
As with all interfacing, we will need to find a common ground. Sometimes we also need to provide power as well. Regardless, this is a small number of signals, especially compared to parallel NAND flash which needs more than 14 connections on a finer pitch package.
Thirdly, although SPI only technically allows a single bus master, we can bend the rules and add another master to directly interact with the flash memory.
Fourthly, NOR flash does not suffer from bad blocks as NAND flash does. The data we read out from the flash will be the same as seen on the filesystem. There is no overhead to handle bad blocks.
Serial Ports
The majority of DVRs will have a serial port on them. These are sometimes called UARTS or USARTS (Universal Synchronous Asynchronous Receiver/Transmitter). This will be a conventional asynchronous serial connection with receive (RX), transmit (TX) and ground (GND). This serial console will often allow access to the bootloader, and sometimes access to the Linux console itself.
RAM
Nearly all DVRs copy data from flash into RAM before executing it. This is why the flash is small (~16Mbytes) and the RAM large (>256MBytes). It would be desirable for us to access the RAM to inspect the OS and see any data the device is processing.
Unfortunately, on these devices, the RAM is DDR3 running at 800MHz or above, using a parallel bus. There is simply no low-cost or accessible means to intercept these signals.
JTAG
It is likely that some DVRs have JTAG on them, but I have had very limited success in interacting with a DVR using it. It would allow flash access, RAM access, and the ability to debug.
Typical DVR
This is a Sansco DVR bought from Amazon in 2020. It is representative of a typical DVR.
In red is the large Hisilicon Hi3520 SoC. I have removed the heatsink, but not the compound holding it on. In blue is the DDR3 RAM. In green is the SPI flash.
The PCB will generally be 4 layers or above. This means that there are layers inside the PCB that you cannot easily see. It is possible for these to carry signals across the board. Most interesting signals will be carried on the surface, with the inner layers reserved for power and ground.
All PCBs will have a solder mask, which is the green layer. This is used to stop solder sticking to places it shouldn’t be. You can generally see traces through the solder mask, and you can push needle probes through this layer to reach traces below.
Most PCBs will have a silkscreen. These are the white letters showing names of components and connectors. The most common letters are:
- R – resistor
- C – capacitor
- L – inductor
- CN – connector
- U – semiconductor
- T – transistor
- X – crystal
Looking at the Hisilicon SoC in more detail, you will note it has pins all around the outside. This is an LQFP package. The signals being accessible around the edge can be extremely helpful when reverse engineering. It has a very fine pitch of 0.4mm – you will struggle to clip or solder to these.
Some DVRs have chips in BGA packages, with the connections under the chip. This can slow down reverse engineering.
To identify pin 1 on a chip such as this, you tend to look for a dot or dimple. You’ll see there are three on this chip – generally, it’s the smallest and deepest one. You can also see a “• 1” marked on the white silkscreen. The logo and text orientation to not have any relevance as to pin 1 – it’s arbitrary.
Next up is the RAM. This will nearly always be in BGA package, physically close to the SoC. There will be a lot of parallel traces going to it, some of which may be “squiggly”. These are called matched-length traces, and are often indicative of RAM. They have to be the same length to ensure that the extremely fast signals arrive at the chip at exactly the same time.
Onto the SPI flash. This will nearly always be in 8 or 16-pin SOIC packages. Part numbers with “25” in them are common, as are binary multiples such as 16, 32, 64, 128, 256 (indicating the size). Manufacturers include Winbond, Spansion, Macronix, and Atmel. The pin-out of the chips is nearly always the same, and the protocol used to communicate with them is very similar. In this case, we have a device made by a smaller company I don’t recognise.
We actually determined that this was the SPI flash partially by elimination. The brand (XMD? XMC?) and part number did not yield good results on google.
The only other 8-pin chips were a small memory (setting and MAC address) and switch-mode power supply ICs. The small memory is an FM24C08D – a 2-wire (or I2C) serial EEPROM, only 8kbytes in size. Not big enough for the firmware!
Nearly all DVRs will have an RTC on them. This is to keep accurate track of the time, even if the power is cycled. We can quickly identify if one is present by two components.
First, they will have a coin cell to provide battery power. Some use different forms, but this is by far the most common.
Second, they will have a 32.768kHz crystal. Why this odd frequency? If you divide it by 2^15, you get one pulse per second – ideal for timekeeping! These crystals are nearly always small cylindrical silver cans.
There will be other crystals to drive other chips – normally the SoC has one at 24MHz, in an oval-shaped can.
Next up is the video ADC (Analog to Digital Converter) or RX (Receiver). There will be one or more of these chips on the board, taking analog video and digitising it. There tends to be one chip for every 4 channels. This is in a QFN (Quad Flat No-leads) package, which means you can just about access the signals around the edge. This part of the board is generally not of security interest though.
Nearly all DVRs will have an Ethernet port. Ethernet is isolated, using a small set of transformers. Often there is a large package near to the port containing these transformers. It is not a chip and is not interesting in security terms.
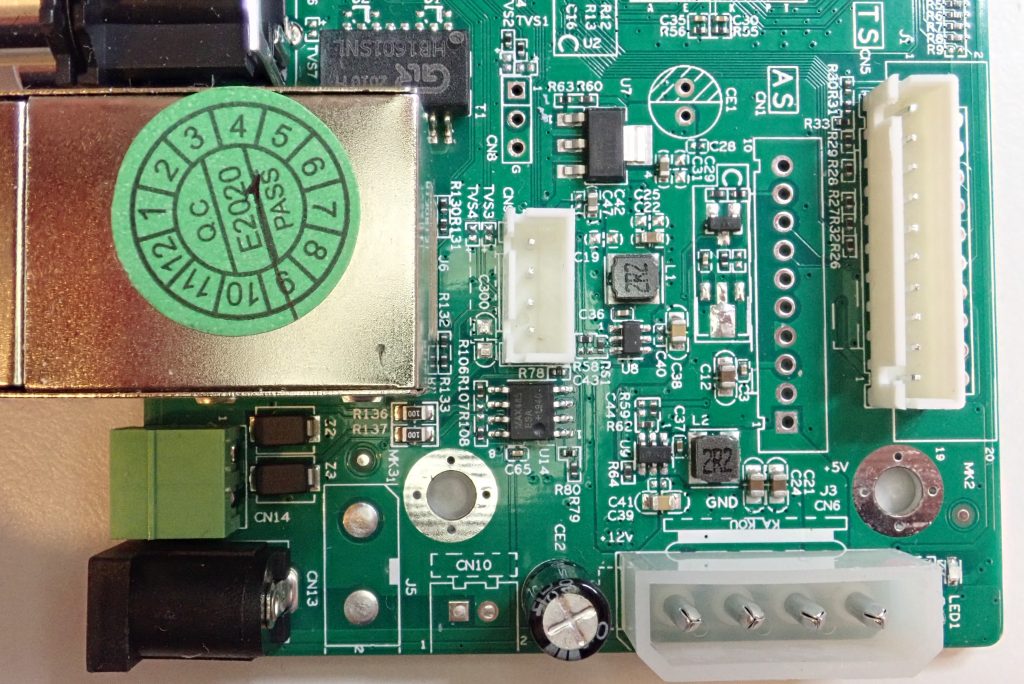
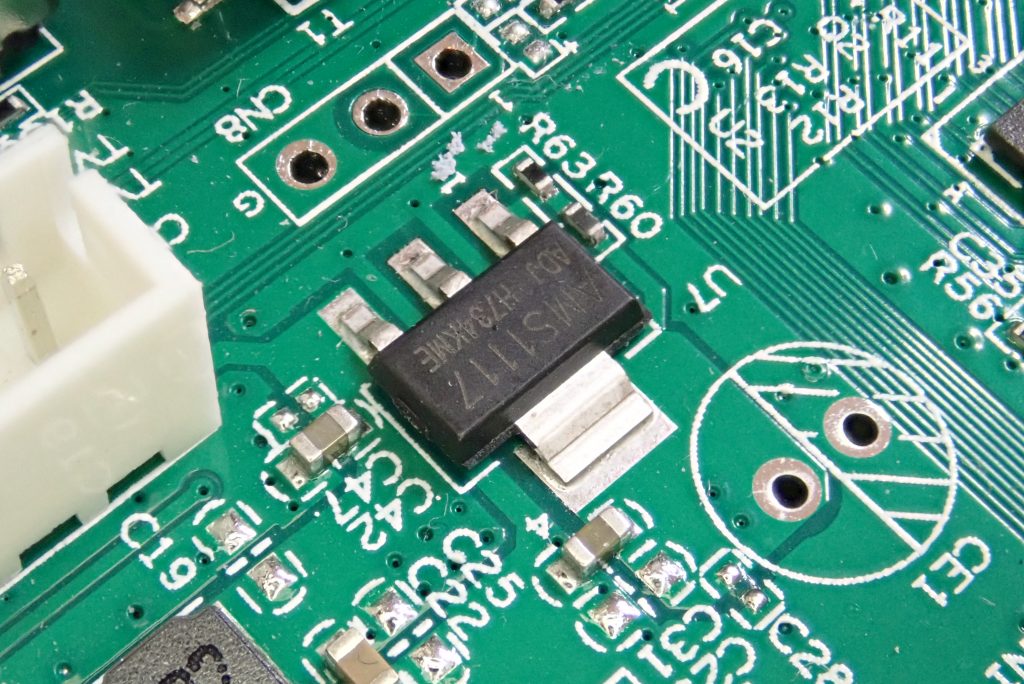
The area near to the power input will be the power supply. There will generally be a switch-mode power supply to drop the voltage down from 12V to 5V, then linear regulators for the 3.3V for the SoC. Again, this has little security relevance to us.
We can quickly isolate power supply areas by looking for certain components. 4-pin packages with one very large tab are normally linear regulators. The large tab allows heat to be conducted onto the PCB to keep it cool.
Large cylindrical capacitors are called electrolytics, and are power reserves, used for smoothing.
Finally, small coils of wire are inductors, very common in switch-mode power supplies. They will be marked with an “L”
Finding serial ports is key. I’ve found that for most DVRs, this will be 3 pin – GND, RX and TX. There is also sometimes a voltage supply as well.
On this DVR it was a 3-pin connector. You can easily make out the ground – it’s the left, pin, connected to the large “ground pour” on the PCB. The other two pins have very fine traces, leading away – likely signals.
Find all the suitable candidates for serial ports when performing an overview of the board. We’ll look into working out if they are serial and how to connect in a later post.
Conclusion
I hope that’s helped in understanding the major components on a DVR. This can be applied to most small embedded devices, but many routers and other IoT now use different forms of flash memory such as eMMC.














Paul M
October 25, 2020 at 7:25pmThis and other recent articles about understanding hardware and finding a serial interface are excellent.. there’s no dumbing down but the explanations are not obscured by jumping too quickly into technical terms.
Michael
October 26, 2020 at 4:31amWhat?! And, no.. quit scaring people by strating out with “hacking” as your main title qoutes but all your article is but of close shots of caps and the general SBC to elaborate your point.. So what they can see my recorded movies and or maybe see my future recordings??!! Whhot feel bad for that “hacker” sitting there waiting for that data!?? This ful of someone who clearly wrote for money..still shots of close up capcitors..
cybergibbons
October 26, 2020 at 7:40amI’m kind of confused. The title is “Identifying Security Relevant Components in a DVR” – it doesn’t mention hacking?
The point of the article is to identify which components matter in security terms. There’s one shot of a capacitor.
But, more to the point, is that the *only* attack you can think of against a DVR? The only impact?
1. Imagine a vulnerable DVR was inside your home, or a school, or a hospital. Would you want those recordings to get out?
2. Imagine a DVR had captured a serious crime, but the password was not known by a forensics team.
3. Imagine the DVR had a backdoor allowing free access onto your home network.
4. Imagine the DVR had the same password as other devices, allowing you to get the password and use it elsewhere.
Maybe think before commenting next time 🙂
David Clacks
February 21, 2021 at 4:45pmI have a dvr system and the dog bit thru the wire one day and that channel no longer will display i believe that the positive may have made contact with the video in how could i get that channel to work again could someone help me with this