Update – if your heating is misbehaving you need to disable port forwarding to port 80 and port 8068. This should be simply following the reverse of whatever you did to set port forwarding up. Alternatively, you could disable WiFi entirely by putting invalid SSID and password in – I believe the thermostats should continue to work.
Contact support@heatmiser.com for an official response.
A while back, I came across a page listing some vulnerabilities on Heatmiser’s Netmonitor product. The Netmonitor is old and discontinued though, so maybe some lessons have been learnt.
I thought I’d take a quick look at the rest of their product line. They have a series of products, generally called WiFi thermostats that connect directly to your router using 802.11b. The products aren’t listed on their site (possibly removed after reporting this), but this Amazon listing gives you an idea.
This is a WiFi thermostat running version v1.2 of the firmware. There are newer versions of the firmware – up to v1.7 as far as I can see.
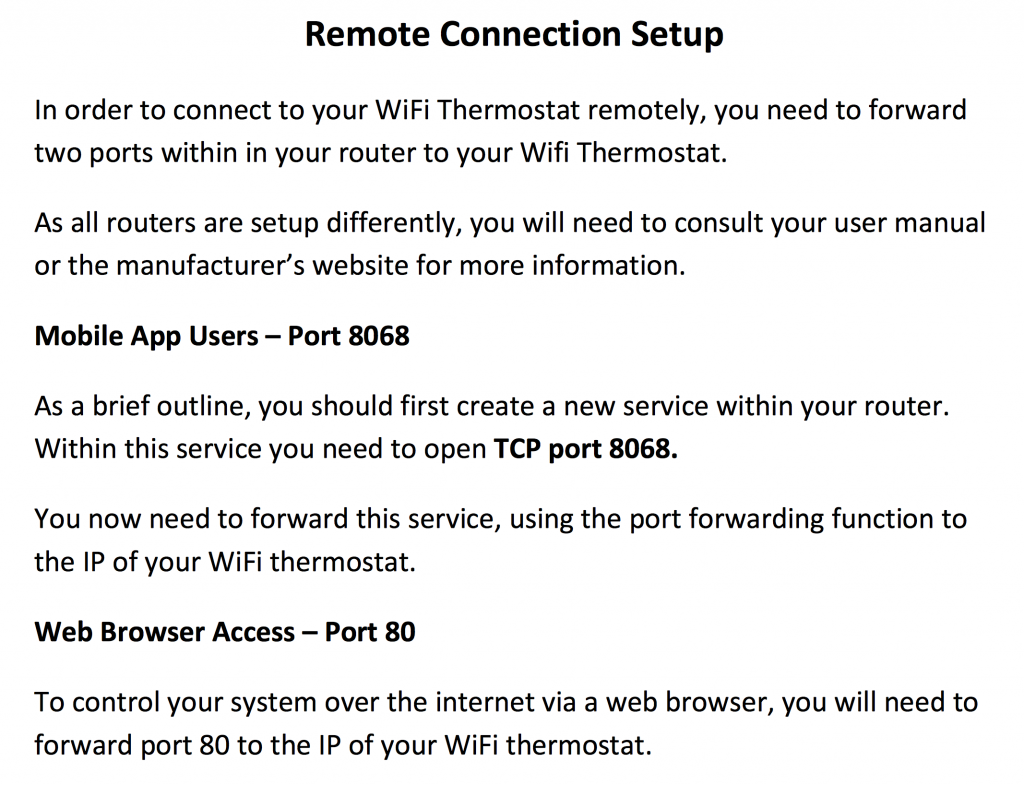
A quick look at the manuals shows that Heatmiser recommend two ports are forwarded to the thermostat from the router- port 80 for web control and port 8068 for app control.
Port forwarding to a small embedded device is an easy way to get access to the device remotely, but it also puts you at risk. That device is now entirely open to the wider Internet on port 80 and 8068.
Also of note – a quick google search for port 8068 shows that the Heatmiser is the most common reason to have port 8068 open. This makes finding Heatmiser thermostats much easier. Scanning for them on port 80 is slow. Port 80 could be any web page, so you need to check for port 80 being open, connect, perform a HTTP request, and then check the content of a web page (e.g. does the title contain “Heatmiser”).
Scanning for Heatmiser thermostats on port 8068 really just requires a quick check for port 8068 being open – we can be fairly confident that anything with this port open is one of their devices. We can then make detailed check on port 80.
nmap -p 8068 -Pn -T 5 --open 78.12.1-254.1-254
nmap can easily do this scan. If you want to scan large blocks of addresses though, masscan is much faster.
However, other people have already done the hard work for us – Shodan search engine scans all IPs, connects to port 80 and records the results. We just need a search term. This is simple – the title of the page is always “Heatmiser Wifi Thermostat”.
Plugging this into Shodan we get over 7000 results. That’s quite a lot. (note, you might need to register to use filters like this).
Issue 1 – default web credentials and PIN
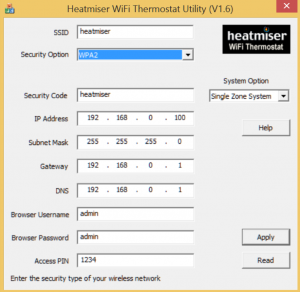
To configure the thermostat, you connect with USB and use a Windows utility. In here you can set the username/password for the web interface and the PIN for port 8068 app access.
The application defaults to admin/admin and PIN 1234.
Even the manual suggests the default username and password.
It’s essential that an internet connected device enforces a custom password of decent strength. This isn’t even suggested or prompted for, never mind enforced.
Heatmiser’s response is that the password should be changed. My response is that their software shouldn’t allow defaults.
Issue 2 – wifi credentials and password can be seen in the plain
When logged into one of the devices, the username, password, WiFi SSID and WiFi password are all filled into the form and can be viewed easily by examine the source of the webpage.
There is really no excuse for this – it’s lazy.
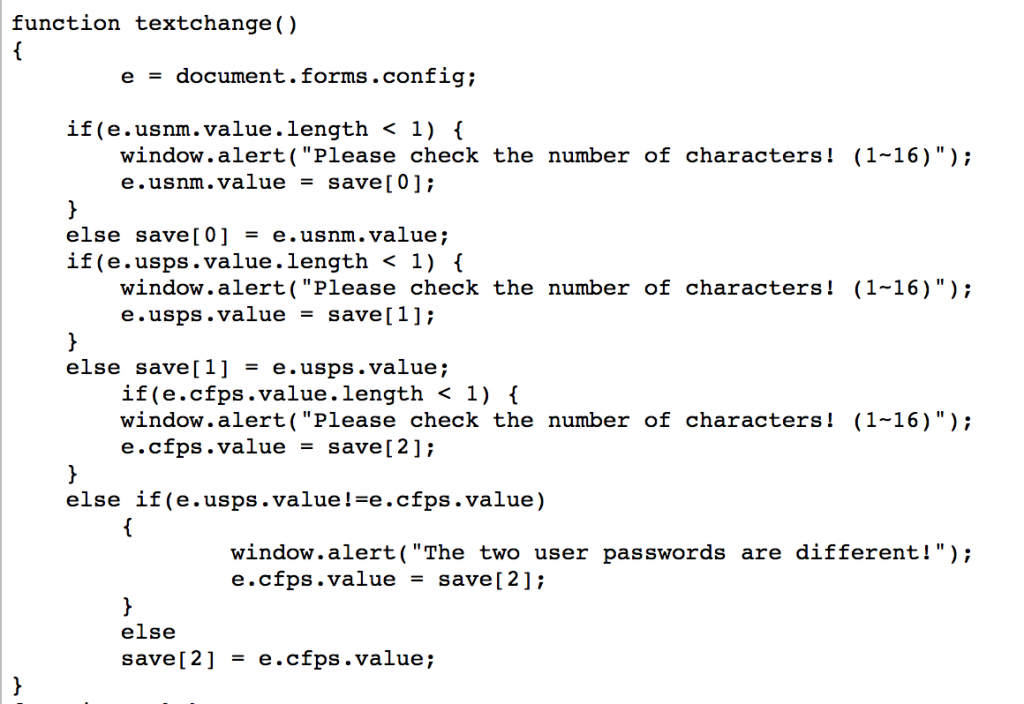
Issue 3 – in-browser user input validation/sanitising
Viewing the source of several pages, it can be seen that the user input input is being validated and sanitised by Javascript.
Why is this an issue? Because often this means no checks are done by the device itself after input is submitted. All you need to do to pass invalid or dangerous data is not use a web-browser to send requests. Use a custom client that performs the same action without the validation.
This opens up many potential attacks.
This seems quite common with low-end processors connected to the Internet. The browser has a lot more power and is a lot more responsive, so checks in-browser often seem attractive.
Issue 4 – open to CSRF attacks
Once logged into the device with a given client (e.g. Chrome), other clients on the same machine can access the device as if they were logged in.
This enables an attack technique called cross-site request forgery. It means that I can send a user a link containing a malicious request and the device will blindly carry it out. For example, I could send a request to change the password to one of my choosing in an email, and as long as the user has logged into the thermostat recently, that request will be carried out by the device.
Best practice would dictate that only requests from pages generated by the device itself would work.
There are a number of ways to protect against CSRF – it’s actually quite complex to do, but this device has no protection at all.
It gets worse though. It appears the authentication works only by IP address. Once the thermostat sees you have logged in from a given IP address, any requests from that IP address will work.
This is a really bad thing to do.
Most homes and workplaces use something called NAT on their routers. This means that all of your laptops, PCs, phones, consoles and tablets all appear to have the same IP to anyone looking from the outside. If I log in to my thermostat from work, it’s likely that the IP address the thermostat sees is also in use by a number of other people.
This means that if I log in to my thermostat at work, anyone else in my workplace can access my thermostat simply by visiting the page without any need for credentials.
As I said, protecting against CSRF is hard but this is as vulnerable as it gets to CSRF.
Issue 5 – no rate limiting or lockout on the port 8068 PIN
The Android and iPhone apps access the device on port 8068 using a custom protocol. Part of this involves sending the 4 digit PIN number to authenticate the app.
A 4 digit PIN only has 10,000 combinations and no username component. This makes brute forcing a PIN number very easy, so it is vital that there is rate-limiting or a lockout e.g. maximum 3 failed PIN attempts followed by a 10 minute lockout.
There is no rate limiting on the WiFi thermostats. You can try about 2 PINs/second over the Internet i.e. going through all 10,000 PINs takes about 1.5hr.
Now and then requests time-out when attempting PINs rapidly, but I suspect this is just a limitation of a low-power embedded device.
Even a fairly conservative lockout of 10 minutes after 3 wrong attempts would increase this to 23 days.
I have written a proof-of-concept to brute force the PIN but don’t want to release it openly currently.
Issue 6 – no means of updating firmware without a physical programmer and taking the device apart
Fixing issues in embedded, Internet connected devices requires a firmware update.
The WiFi thermostat appears to have no way of doing this remotely or via the web interface. It requires borrowing a programmer from Heatmiser (after paying a deposit), removing the device from the wall and updating it.
This is such a large barrier that very few people are going to do it. This creates an ethos and dynamic where neither the company or the customer is driven to fix or deploy security issues. The source for this little nugget of info started from this page here – where someone describes the process in the comments.
Issue 7 – trivial web authentication bypass
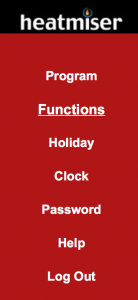
Go to the IP of any Heatmiser thermostat in a browser and you get the login box (often along with an annoying Javascript pop-up telling you the username/password is wrong for no reason).
Give it the right password and you end up on a framed window with several bits of HTML.
Each one of these frames is a .htm file. Trying each of these one by one, it’s found that left.htm can always be accessed regardless of the login status. This is the left hand menu.
From here all of the menu items work fine (even if the individual .htm files didn’t work directly).
You can go to the “Password” page, view the source, and then recover the password and login normally.
This means that gaining remote access to these thermostats is as easy as going to:
http://87.56.123.121/left.htm
This is really not good.
Edit – the reason this happens is that the Javascript redirect (issue 8 below) has an error in it on left.htm…
Issue 8 – part of the authentication is Javascript based (up to v1.7)
Most of the thermostat pages have this little Javascript snippet on them:
if(document.logfm.lgst.value != "1") top.location.href="index.htm";
This checks to see if you are logged in. If you aren’t, you get redirected back to the login page.
This would be a great idea if the same piece of HTML didn’t also include the content that you aren’t supposed to see.
You are letting the bad guys in regardless, and hoping you kick them out quickly enough not to see anything.
All you need to do to view the protected pages – including the one with the password in the open – is view the page in a browser with Javascript turned off, or use wget.
wget http://86.34.23.78/networkSetup.htm
This is amongst the most awful security design I have ever seen.
Issue 9 – commands are carried out by unauthenticated HTTP POST
Most people who use a web browser will be familiar with HTTP GET to send data to the server at the other end. Google queries are the most obvious:
https://www.google.co.uk/search?q=heatmiser+is+pwned
There is another mechanism called POST. You don’t see these in the URL like GET, but the idea is very similar.
All you need to do to change settings on the thermostat is send a POST request. No password required.
The barrier to entry here is that you can’t just type POST requests into the URL bar. But it isn’t exactly hard.
POST /statSetup.htm HTTP/1.1 Host: 70.129.58.10 User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.9; rv:32.0) Gecko/20100101 Firefox/32.0 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8 Accept-Language: en-US,en;q=0.5 Accept-Encoding: gzip, deflate Referer: http://70.129.58.10/statSetup.htm Connection: keep-alive Content-Type: application/x-www-form-urlencoded Content-Length: 32 setT=01%3A01&setD=01%2F01%2F2000
That’s just a grab from Burp Suite sending a request to a thermostat to change the time.
But you can seemingly change any setting.
Conclusion
I’ve stopped looking for issues at this point. There are probably a wealth of other things that could be worth investigating, including:
- Fuzzing the port 8068 input. Custom protocols are often vulnerable to malformed inputs causing crashes
- Hidden webpages
- Backdoor accounts
- Firmware inspection
But, at this point, it looks like security is the last thing on the list of priorities for Heatmiser.
If you want a thermostat that can’t be activated by just about anyone, then I would suggest returning your Heatmiser WiFi thermostat.
My recommendation would be to stop port-forwarding to both port 80 and 8068. You will lose remote control, but would still be able to access the thermostat from inside your house.
You can contact Heatmiser on support@heatmiser.com if you need help dealing with this.
Heatmiser’s response
I emailed Heatmiser to inform them of these issues.
I believe they must have been aware of some or all of these issues before now, and due to the severity and basic nature of the issues, I decided to follow full disclosure.
They have responded as follows:
Thank you for your email.We are investigating the issues you mention and will provide an update to fix the security issues you highlight. We will advise customers in the meantime to close port 80 on their WiFi Thermostat until the issue has been rectified.Once again, thank you for bringing this to our attention.
Heatmiser’s solution
Heatmiser have sent an email/letter out to customers. They have two options – replace the thermostat with one without a web interface and with rate limiting on the pin, or get a refund.
I’m surprised there is no attempt to fix the web interface.
Here is the Letter from Heatmiser sent out.




Kemp
September 20, 2014 at 10:20amI love these investigation type posts, and it looks like this one was just asking for it. It’s hard to imagine a product design process that includes “let’s instruct the user to make the device publicly accessible over the internet, they love doing things remotely, but let’s not enforce any kind of security because that just annoys people”. I think this is pretty much the end-marker for one side of the convenience-security trade off, it just needs to register its IP and pin with a central publicly accessible database to finish the job off 🙂
cybergibbons
September 20, 2014 at 10:28amI was hoping I’d have to work a little harder. They may well be ways of not having to authenticate at all. I’d really need a couple of devices in front of me to take a look and I don’t want to spend any more money on embedded systems at the moment.
It’s sad how bad most of these systems are.
Kemp
September 20, 2014 at 8:26pmI have one word for that update: wow. I hope they got a couple of interns to write the code and then ran no QA on it, because the alternative is that it was written (and signed off) by professionals.
cybergibbons
September 20, 2014 at 9:59pmYeah – I actually can’t work out how they allowed a single page to work without auth and act as a gateway to the others.
alex
September 21, 2014 at 3:48pmI suspect it simply checks HTTP REFERER, you could test this by faking up a different referrer and seeing if it still works.
cybergibbons
September 21, 2014 at 5:14pmYes – I just need to sit down and try this.
Gary
September 21, 2014 at 4:18pmJust tested v1.7 of heatmiser’s software and at initial glance directly linking to any .htm file takes you to the login screen. But if you view source of the .htm file it is actually all there and javascript is redirecting you. That means by looking at /networkSetup.htm you can see the username and password in plain text.
I think this deserves a call to Heatmiser to demand a full refund as the product is not fit for purpose. Fortunately I don’t expose the html interface to the internet, however the pin code brute force is a concern.
cybergibbons
September 21, 2014 at 5:13pmOuch. Not seen any 1.7 in the wild!
Gary
September 21, 2014 at 5:32pmThis one was purchased in March.
cybergibbons
September 21, 2014 at 6:50pmHoly crap.
Yes – it sends the HTML with all of the details and JavaScript kicks you back.
This is so shoddy – thanks for the work finding that.
cybergibbons
September 22, 2014 at 8:22amKeep me updated on the refund process.
I think the level of failure here is totally unacceptable and indicates a total disregard to customer’s security, privacy and safety. It’s not just mistakes made when implementing a secure system, it’s shortcuts taken at the design stage.
I’d also be extremely cautious if buying any newer products like the Neo, as this kind of failure comes from company ethos/attitude, not just making a few mistakes.
Gary
September 22, 2014 at 11:57amJust called heatmiser and spoke to “chief technical person”. They have only become aware of it this morning and have told everyone on their mailing list to close port 80. Meanwhile they are working on a fix, but “it only affects a certain webbrowser”. Clearly chief technical person does not understand and then he proceeded to claim he was not a software engineer and did not understand the full details.
It worries me that they could implement this and not realise it was insecure. This should not be news to them!
It might be news to @BBCRoryCJ and @BBCTech!
JLP
September 22, 2014 at 1:12pmI send my first security advisory january 7, 2013 with no reply their side. You can find my twwet about it. (Jean-Louis PERSAT @TheCodingFrog 7 janv. 2013
For #security reason everyone using #heatmiser thermostat should block web admin to WAN access, or at least put any port other than 80)
I still have the scanner I’ve coded to log IP of Heatmiser thermostats 🙂
At this time they do not take it into consideration.
cybergibbons
September 22, 2014 at 1:16pmSo I see!
I wonder why they have buried their heads so long?
https://twitter.com/TheCodingFrog/status/288379701574115329
JLP
September 22, 2014 at 4:12pmBecause they are unskilled. I think they came from oldschool electronics devices and they don’t really know much about IT.
Take a look at a mail from their support team, it makes me ROFL :
“Hi,
There is no no security risk as only you will be aware of what your ip address is.
Regards
Ruth”
So I decided to scan and send them some IP as proof.
Two years since I wait they take this into consideration with no luck.
cybergibbons
September 22, 2014 at 4:25pmHmm. Not good! Did Shodan exist back then?
This problem seems fairly pervasive amongst small companies. I’m not asking for perfect security but at least some security.
Researcher Discloses Wi-Fi Thermostat Vulnerabilities | Threatpost | The first stop for security news
September 22, 2014 at 8:47pm[…] by night,” whose specialty is digging up bugs in embedded systems wrote on his blog cybergibbons.com, that he initially read about vulnerabilities in another one of the company’s products, […]
Researcher Discloses Wi-Fi Thermostat VulnerabilitiesDigital Era | Digital Era
September 22, 2014 at 10:01pm[…] by night,” whose specialty is digging up bugs in embedded systems wrote on his blog cybergibbons.com, that he initially read about vulnerabilities in another one of the company’s products, […]
Jules
September 23, 2014 at 1:53pmWhile I do think it’s great to name and shame rubbish companies regarding security. A day after your article is released my heating is hacked. 6am at 35 degrees! As you already have explained, they seem uninterested.
VPN I think is the only solution for this and other similar insecure systems.
cybergibbons
September 23, 2014 at 1:56pmThanks for leaving a comment.
I spent some time weighing up disclosing the issues in full and felt that a lack of response in the past meant nothing would be done otherwise. I hope the inconvenience to some will be offset by improvements to security.
IoT has a long way to come in security terms.
Heatmiser WiFi thermostats leak passwords, plagued by vulnerabilities
September 23, 2014 at 4:48pm[…] the vulnerabilities were brought to Heatmiser’s attention by bug hunter Andrew Tierney who documented the various problems he found with the devices, and discovered over 7000 vulnerable thermostats connected to the […]
ste williams – Heatmiser digital thermostat users: For pity’s sake, DON’T SWITCH ON the WI-FI
September 24, 2014 at 12:53pm[…] discovered that when users connect the thermostat via a Windows utility it uses default usernames and PINs […]
Sam
September 25, 2014 at 12:48amThanks for doing this. I needed an example to show my peers of how vulnerable network connected devices can be. Being able to say “just imagine he’s talking about your (product x) instead of a thermostat.
I connected the dots, by the way. It’s easy to get a list of all these devices, everywhere in the world. And, with a single POST you could turn all of them up, instantly. Terrible.
Your Thermostat Can Be A Gateway For Criminals To Break Into Your Home - Aveir Technology Aveir Technology
September 29, 2014 at 4:49pm[…] Andrew Tierney, a security expert with cybergibbons.com, did some research on the Heatmiser products and found some 7000 unprotected thermostats reported on many hacker forums and websites. Many of the reported thermostats on the hacker websites were in Europe, but this doesn’t mean that incidents of criminal activity are limited to across the pond. […]
Very Dumb Security For a WiFi Thermostat
September 29, 2014 at 8:00pm[…] thermostat, but you have no idea how bad the security can be for some of these devices. The Heatmiser WiFi thermostat is probably the worst of the current round of smart home devices, allowing anyone with even a tiny […]
Your Thermostat Can Be A Gateway For Criminals To Break Into Your Home - LAN Infotech LAN Infotech
September 30, 2014 at 1:15am[…] Andrew Tierney, a security expert with cybergibbons.com, did some research on the Heatmiser products and found some 7000 unprotected thermostats reported on many hacker forums and websites. Many of the reported thermostats on the hacker websites were in Europe, but this doesn’t mean that incidents of criminal activity are limited to across the pond. […]
Your Thermostat Can Be A Gateway For Criminals To Break Into Your Home « SnapBack Solutions SnapBack Solutions
September 30, 2014 at 1:52am[…] Andrew Tierney, a security expert with cybergibbons.com, did some research on the Heatmiser products and found some 7000 unprotected thermostats reported on many hacker forums and websites. Many of the reported thermostats on the hacker websites were in Europe, but this doesn’t mean that incidents of criminal activity are limited to across the pond. […]
Your Thermostat Can Be A Gateway For Criminals To Break Into Your Home « Onserve Onserve
September 30, 2014 at 2:06am[…] Andrew Tierney, a security expert with cybergibbons.com, did some research on the Heatmiser products and found some 7000 unprotected thermostats reported on many hacker forums and websites. Many of the reported thermostats on the hacker websites were in Europe, but this doesn’t mean that incidents of criminal activity are limited to across the pond. […]
Very Dumb Security For a WiFi Thermostat | Hack The Planet
September 30, 2014 at 3:53am[…] thermostat, but you have no idea how bad the security can be for some of these devices. The Heatmiser WiFi thermostat is probably the worst of the current round of smart home devices, allowing anyone with even a tiny […]
Your Thermostat Can Be A Gateway For Criminals To Break Into Your Home - Bold Tech Solutions Bold Tech Solutions
October 22, 2014 at 11:55am[…] Andrew Tierney, a security expert with cybergibbons.com, did some research on the Heatmiser products and found some 7000 unprotected thermostats reported on many hacker forums and websites. Many of the reported thermostats on the hacker websites were in Europe, but this doesn’t mean that incidents of criminal activity are limited to across the pond. […]
The Internet of Things is gathering pace, but shortcuts can be costly » Cambridge Consultants
November 27, 2014 at 8:10am[…] Of Things (IoT) devices. The list of devices that have been hacked is pretty long already – Thermostats, TVs, Printers, Light Bulbs, Webcams – and the technology is still in its infancy. It strikes […]
Your Thermostat Can Be A Gateway For Criminals To Break Into Your Home - Paragon Paragon
December 21, 2014 at 5:38pm[…] Andrew Tierney, a security expert with cybergibbons.com, did some research on the Heatmiser products and found some 7000 unprotected thermostats reported on many hacker forums and websites. Many of the reported thermostats on the hacker websites were in Europe, but this doesn’t mean that incidents of criminal activity are limited to across the pond. […]
Your Thermostat Can Be A Gateway For Criminals To Break Into Your Home | CSP
January 13, 2015 at 8:58pm[…] Andrew Tierney, a security expert with cybergibbons.com, did some research on the Heatmiser products and found some 7000 unprotected thermostats reported on many hacker forums and websites. Many of the reported thermostats on the hacker websites were in Europe, but this doesn’t mean that incidents of criminal activity are limited to across the pond. […]
Your Thermostat Can Be A Gateway For Criminals To Break Into Your Home - Ten Feet Ten Feet
January 25, 2015 at 2:34am[…] Andrew Tierney, a security expert with cybergibbons.com, did some research on the Heatmiser products and found some 7000 unprotected thermostats reported on many hacker forums and websites. Many of the reported thermostats on the hacker websites were in Europe, but this doesn’t mean that incidents of criminal activity are limited to across the pond. […]
Gary
January 26, 2015 at 5:03pmI’ve written a secure web interface for a heatmiser that can be run on a NAS drive behind the internet firewall. Available here:
http://www.fogma.co.uk/foggylog/archive/382.html
Eventually I’ll also make my php logging and graphing software available as well. It plots pretty graphs of house temperature, temperature setpoint, external temperature and when the heating is active.
Gary
Your Thermostat Can Be A Gateway For Criminals To Break Into Your Home - MIT Consulting MIT Consulting
February 1, 2015 at 12:41am[…] Andrew Tierney, a security expert with cybergibbons.com, did some research on the Heatmiser products and found some 7000 unprotected thermostats reported on many hacker forums and websites. Many of the reported thermostats on the hacker websites were in Europe, but this doesn’t mean that incidents of criminal activity are limited to across the pond. […]
Your Thermostat Can Be A Gateway For Criminals To Break Into Your Home - Palisades Palisades
February 13, 2015 at 1:24am[…] Andrew Tierney, a security expert with cybergibbons.com, did some research on the Heatmiser products and found some 7000 unprotected thermostats reported on many hacker forums and websites. Many of the reported thermostats on the hacker websites were in Europe, but this doesn’t mean that incidents of criminal activity are limited to across the pond. […]
Your Thermostat Can Be A Gateway For Criminals To Break Into Your Home | ulistic-projects.com
March 1, 2015 at 5:32pm[…] Andrew Tierney, a security expert with cybergibbons.com, did some research on the Heatmiser products and found some 7000 unprotected thermostats reported on many hacker forums and websites. Many of the reported thermostats on the hacker websites were in Europe, but this doesn’t mean that incidents of criminal activity are limited to across the pond. […]
Your Thermostat Can Be A Gateway For Criminals To Break Into Your Home - 24unet 24unet
March 1, 2015 at 7:34pm[…] Andrew Tierney, a security expert with cybergibbons.com, did some research on the Heatmiser products and found some 7000 unprotected thermostats reported on many hacker forums and websites. Many of the reported thermostats on the hacker websites were in Europe, but this doesn’t mean that incidents of criminal activity are limited to across the pond. […]
Your Thermostat Can Be A Gateway For Criminals To Break Into Your Home « Cat-Tec Cat-Tec
March 3, 2015 at 11:24pm[…] Andrew Tierney, a security expert with cybergibbons.com, did some research on the Heatmiser products and found some 7000 unprotected thermostats reported on many hacker forums and websites. Many of the reported thermostats on the hacker websites were in Europe, but this doesn’t mean that incidents of criminal activity are limited to across the pond. […]
Your Thermostat Can Be A Gateway For Criminals To Break Into Your Home « Thriveon Thriveon
March 10, 2015 at 8:35am[…] Andrew Tierney, a security expert with cybergibbons.com, did some research on the Heatmiser products and found some 7000 unprotected thermostats reported on many hacker forums and websites. Many of the reported thermostats on the hacker websites were in Europe, but this doesn’t mean that incidents of criminal activity are limited to across the pond. […]
Your Thermostat Can Be A Gateway For Criminals To Break Into Your Home - Computer Masters Computer Masters
April 19, 2015 at 5:04am[…] Andrew Tierney, a security expert with cybergibbons.com, did some research on the Heatmiser products and found some 7000 unprotected thermostats reported on many hacker forums and websites. Many of the reported thermostats on the hacker websites were in Europe, but this doesn’t mean that incidents of criminal activity are limited to across the pond. […]
Your Thermostat Can Be A Gateway For Criminals To Break Into Your Home - Lenius Technologies Lenius Technologies
May 26, 2015 at 4:36pm[…] Andrew Tierney, a security expert with cybergibbons.com, did some research on the Heatmiser products and found some 7000 unprotected thermostats reported on many hacker forums and websites. Many of the reported thermostats on the hacker websites were in Europe, but this doesn’t mean that incidents of criminal activity are limited to across the pond. […]
Your Thermostat Can Be A Gateway For Criminals To Break Into Your Home - DFW IT GUYS
August 24, 2015 at 2:15pm[…] Andrew Tierney, a security expert with cybergibbons.com, did some research on the Heatmiser products and found some 7000 unprotected thermostats reported on many hacker forums and websites. Many of the reported thermostats on the hacker websites were in Europe, but this doesn’t mean that incidents of criminal activity are limited to across the pond. […]
Your Thermostat Can Be A Gateway For Criminals To Break Into Your Home – SMB CloudTech
August 30, 2016 at 8:19pm[…] Andrew Tierney, a security expert with cybergibbons.com, did some research on the Heatmiser products and found some 7000 unprotected thermostats reported on many hacker forums and websites. Many of the reported thermostats on the hacker websites were in Europe, but this doesn’t mean that incidents of criminal activity are limited to across the pond. […]
IoT SmartHouse – Alguien entro a mi casa desde Internet. – CyberSecurityLabs
September 28, 2016 at 8:47am[…] Acá encontré un investigador que ya hablo de esto:http://cybergibbons.com/security-2/heatmiser-wifi-thermostat-vulnerabilities/ […]